Centralized hub for the enterprise admin 🛠️
PROJECT OVERVIEW
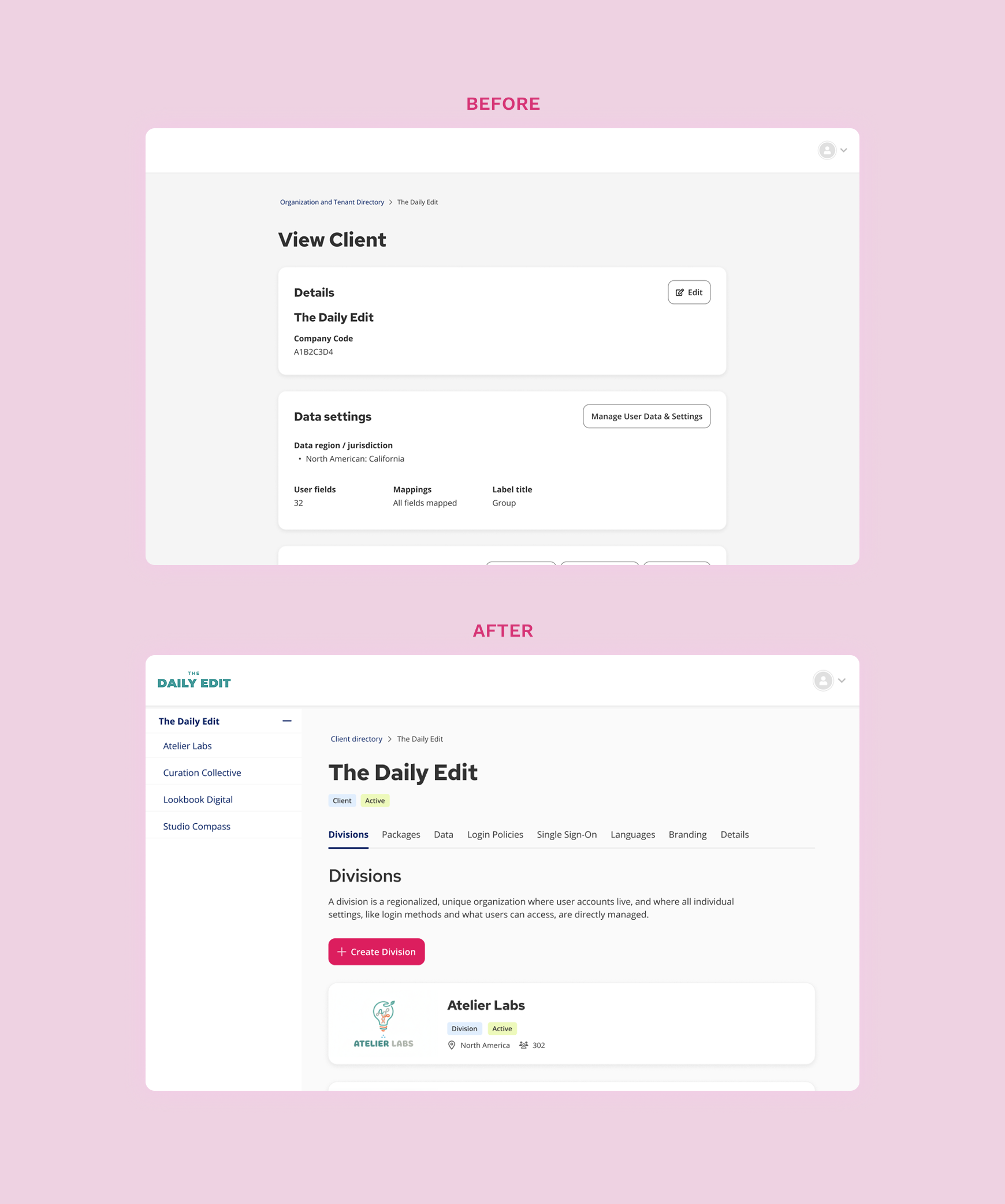
The Benevity platform was undergoing a critical shift with the implementation of Auth0, requiring a massive redesign of the internal admin portal to support a new organizational hierarchy. My role as the lead product designer of User Identity & Access Management was to transform this legacy, unscalable system into a centralized, object-oriented hub.
EMPLOYER
Benevity – the leading corporate social responsibility (CSR) SaaS platform used by large enterprises to manage employee giving, volunteering, and grants to drive social impact.
2024 - PRESENT // PARTIALLY LAUNCHED
The challenge: designing for enterprise complexity 🤯
Our core challenge stemmed from a platform-wide migration to Auth0 for user authentication. While this streamlined the client-facing login experience (supporting both SSO and local login), it exposed a critical limitation in our legacy internal admin portal: it could not support the new, required organizational hierarchy.
The legacy system was:
Inflexible: It lacked support for the new client (parent) and division (child) relationship model.
Unscalable: It was not designed to accommodate the increasing number of configurations and new platform products being added.
Slow: The existing data fetching logic resulted in unacceptable load times for our internal administrators.
We needed to build a new, highly scalable central hub for internal admins to configure all authentication/authorization settings (SSO, MFA, roles & permissions), global Client settings (branding, product modules), and user management.
———
Design process 🧭
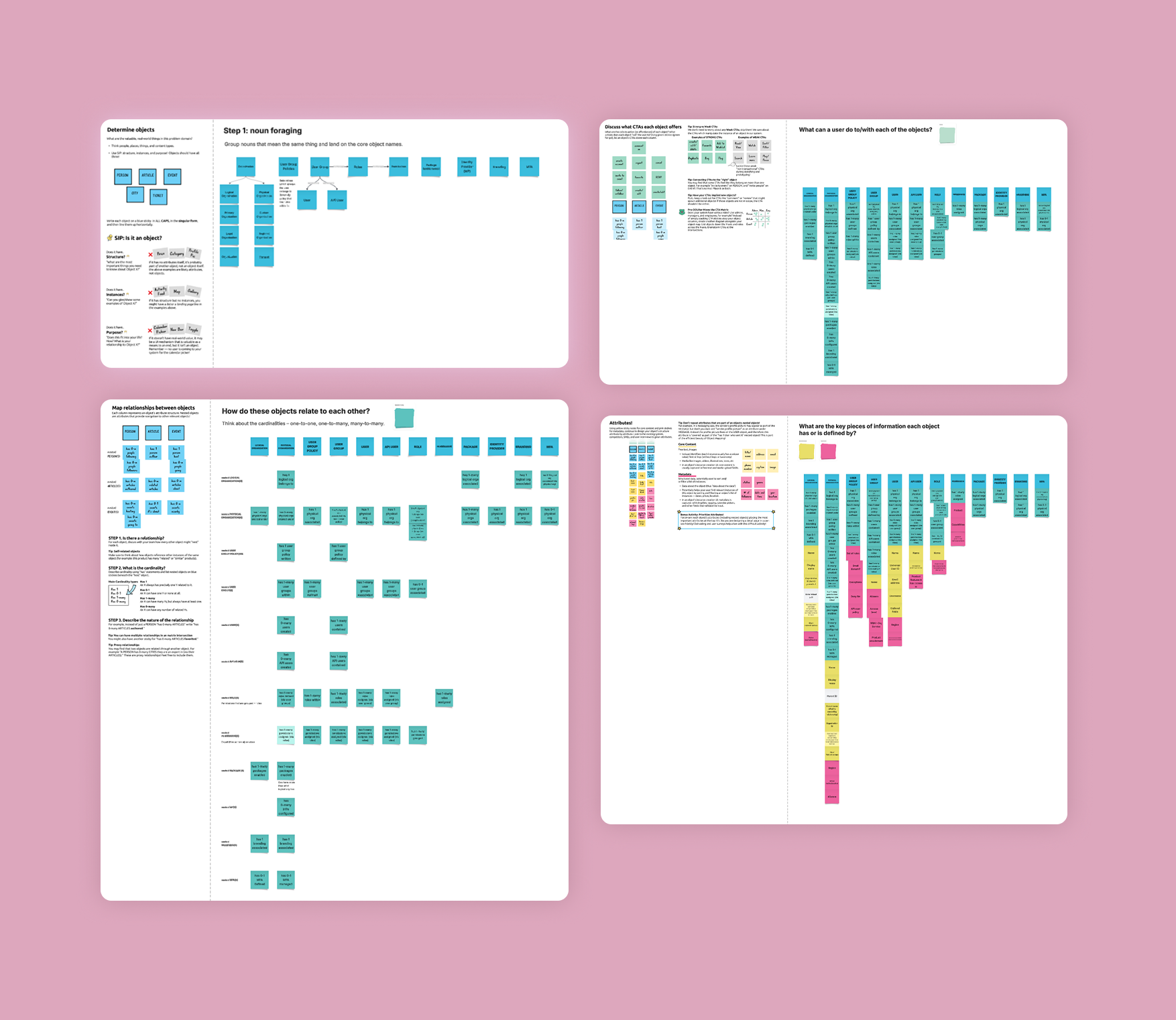
STEP ONE: DEFINING THE INFORMATION ARCHITECTURE WITH OOUX
To establish a shared mental model and prevent technical debt, I ran an Object-Oriented UX (OOUX) workshop with our cross-functional Product and Engineering teams. This work was essential for defining the platform's foundation:
Object naming: Defining standardized, consistent names for all core elements (e.g., Client, Division, User).
Relationship mapping: Clearly defining the nested, hierarchical relationship between the parent client and child division objects.
Defining CTAs: Identifying and standardizing the primary actions admins needed to take for each object.
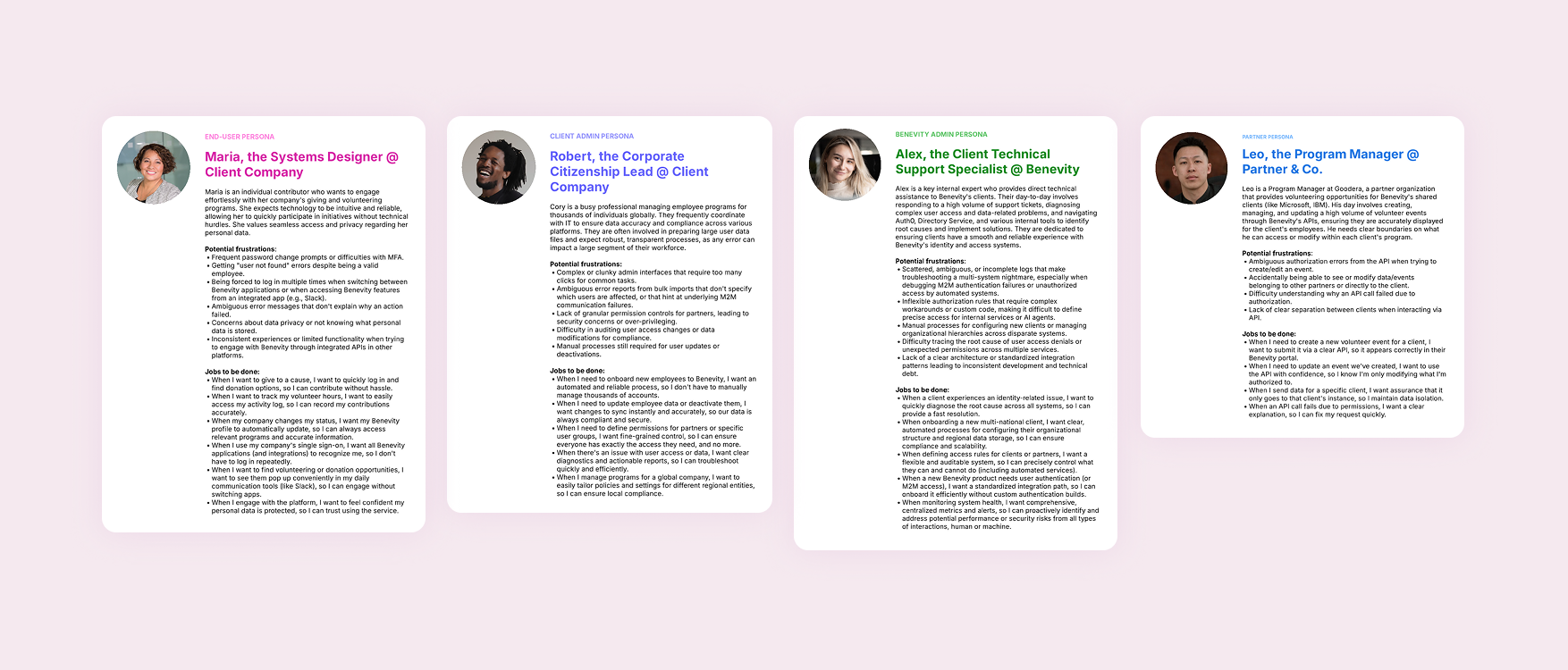
STEP TWO: UNDERSTAND USER NEEDS
We defined key user personas for our internal admins (End-User, Client Admin, Benevity Admin, Partner). This step helped us prioritize design decisions based on their daily Jobs To Be Done (JTBD) in the Benevity ecosystem, ensuring the workflows were optimized for frequency and criticality.
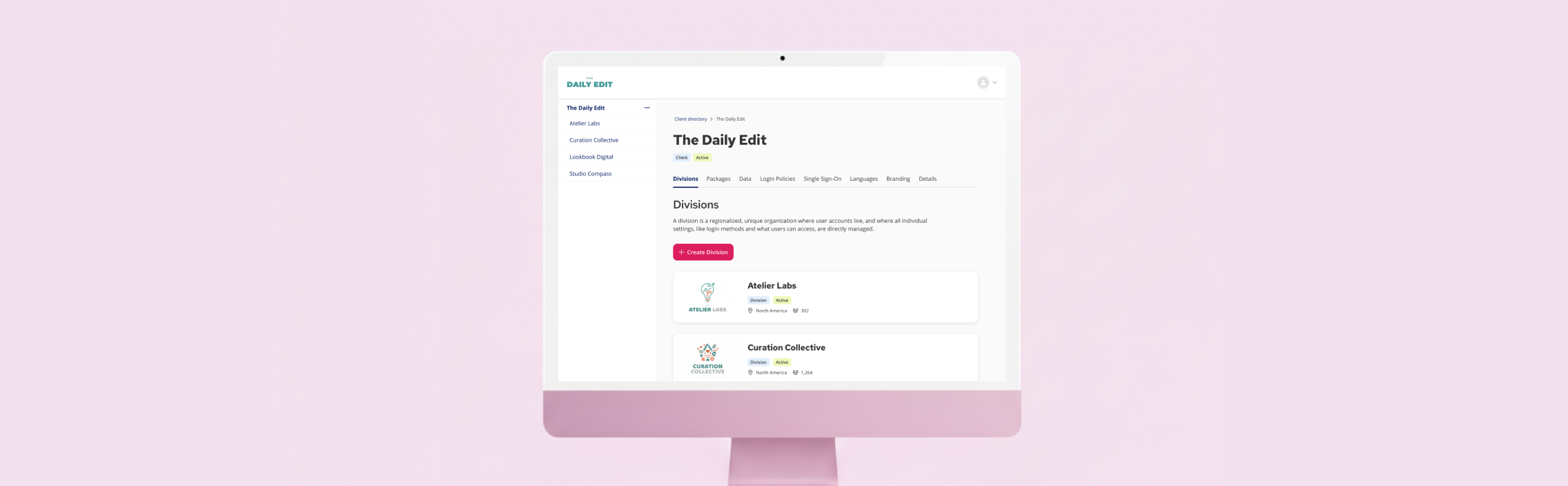
STEP THREE: STRUCTURING THE EXPERIENCE
I led the iteration on the new navigational hierarchy and data visualization patterns. The primary goal was to clearly demonstrate the parent-child relationship between clients and divisions, and to provide intuitive workflows for global administration versus granular division-level actions.
———
The solution: a scalable, object-oriented admin portal 💡
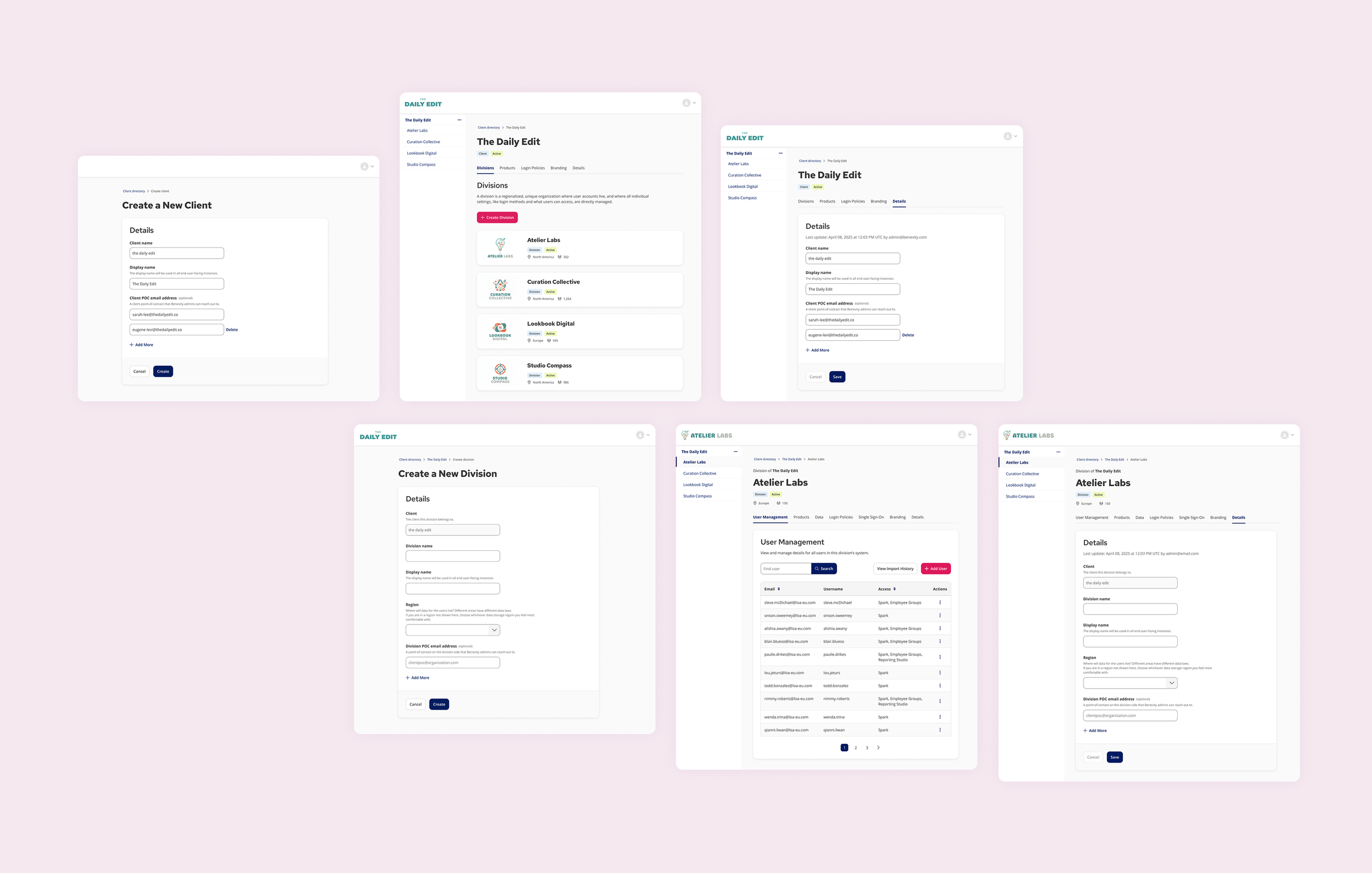
The new system established a single source of truth for all enterprise client configurations. By architecting the platform around the parent-child relationship, we achieved an experience that was:
Granular: Settings could be applied precisely at the client level, with Divisions retaining the necessary flexibility for overrides.
Efficient: The new structure provided the foundation for engineering to implement optimized data fetching, resulting in significant performance gains.
Future-proof: The design supports future expansion of both clients and configurable settings, with the long-term goal of exposing this control panel to client admins to allow for self-service configuration, thus removing a large burden from our internal teams.
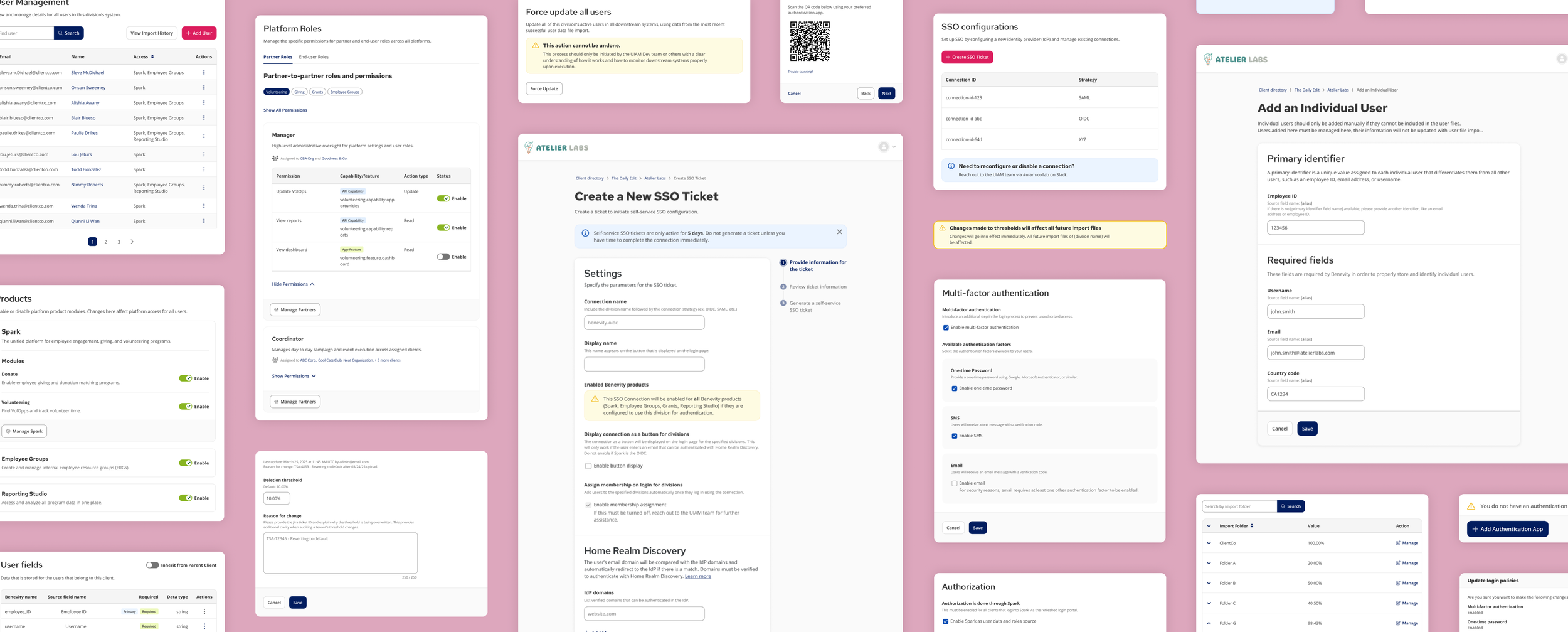
ORGANIZATIONAL MANAGEMENT
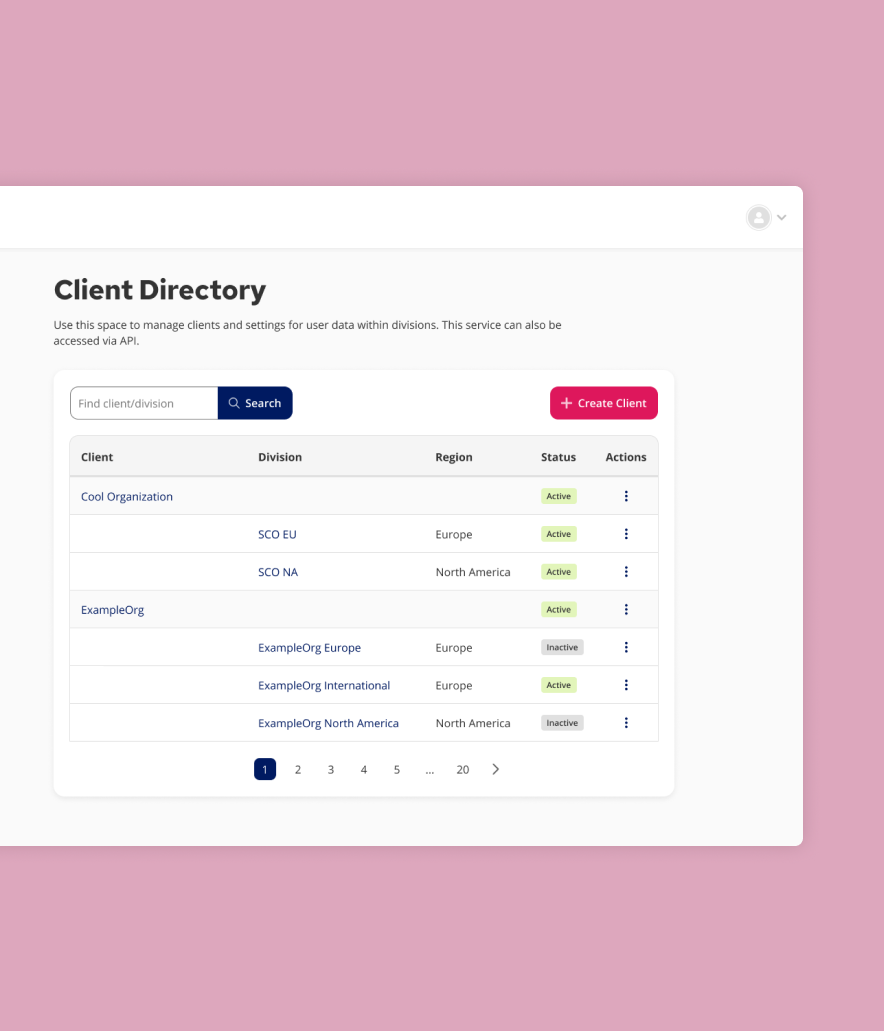
Ability to view all clients and divisions in a unified directory.
Workflows to create, manage, and edit both new and existing clients and divisions.
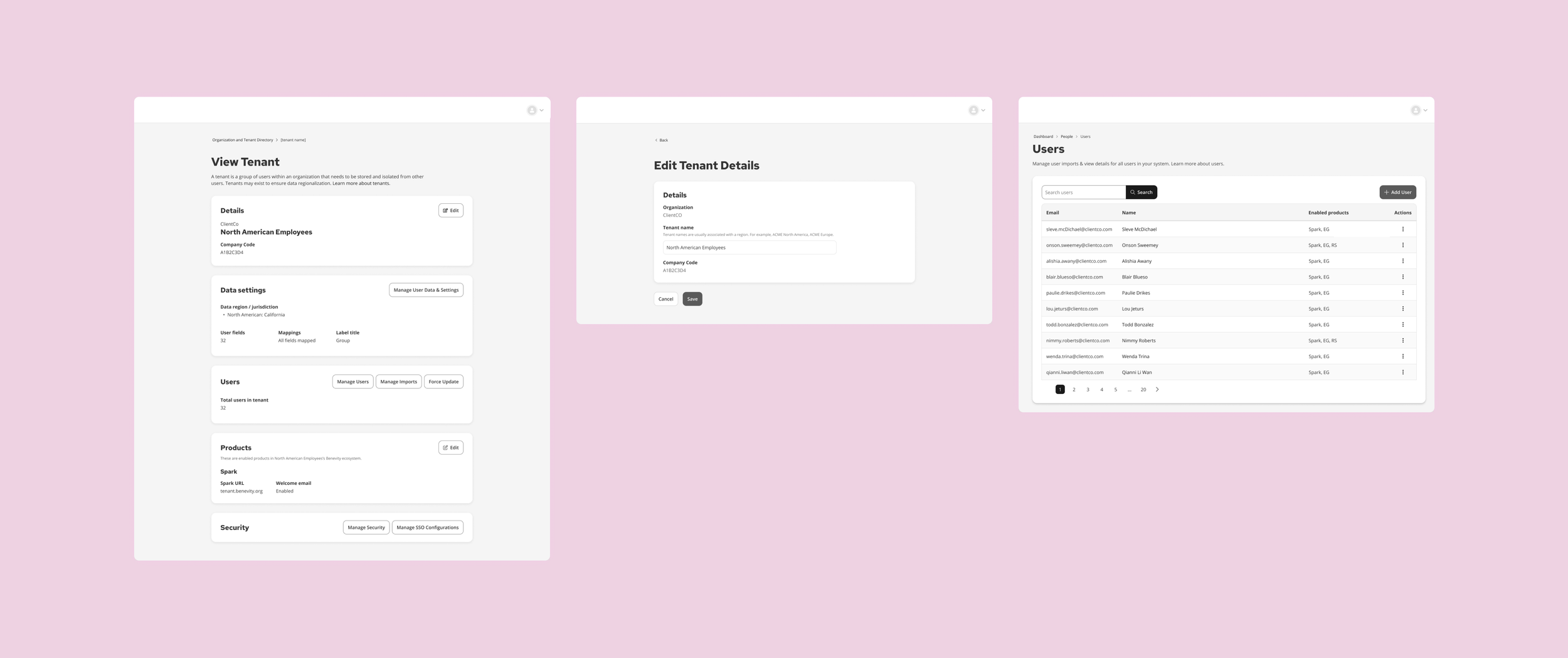
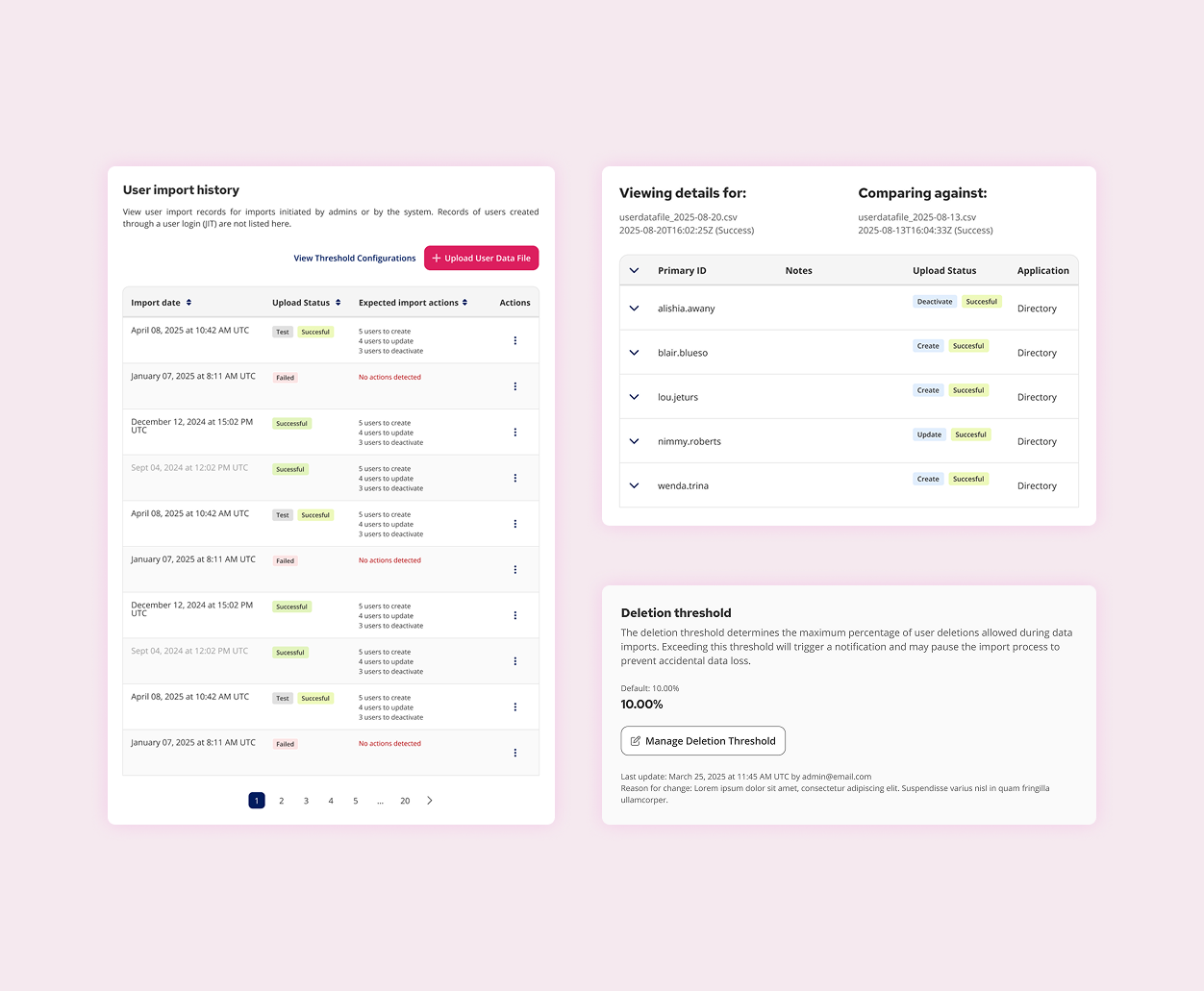
USER & DATA MANAGEMENT
Comprehensive views for viewing, adding, and editing individual user records.
Tools for user data file uploads, including a detailed history of past uploads.
A change comparison feature to view differences between the new file and the existing data.
Configuration of threshold overrides for user data file uploads to prevent catastrophic errors.
AUTHENTICATION, AUTHORIZATION, AND SECURITY
Tools to enable, set, and manage MFA (Multi-Factor Authentication) settings.
Full configuration suite to enable and set up SSO (Single Sign-On) connections, including necessary metadata uploads and troubleshooting features.
User group roles & permissions: Implemented a granular system to define and assign roles to user groups, ensuring the correct internal teams have the right level of access (view-only vs. administrative control) within the Admin Portal.
Management of Authorization (AuthZ) settings to define internal user access and platform permissions.
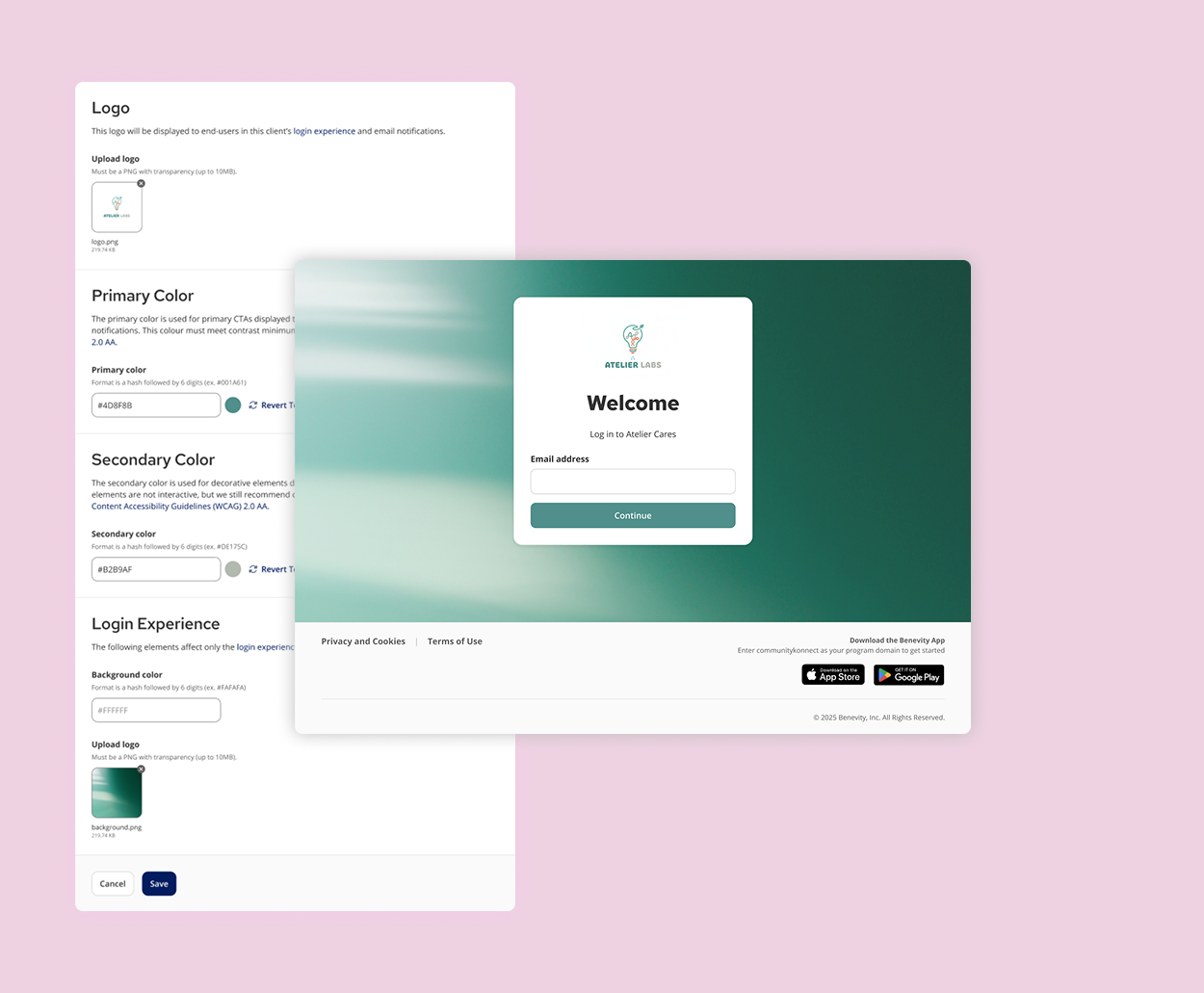
GLOBAL & PRODUCT CONFIGURATIONS
Interface to add client-specific branding
Toggles and selectors to enable product modules based on the client's purchased platform package subscription.
———
Key outcomes 🎯
As this is a foundational infrastructure and security project supporting internal users, the key metrics focused on operational improvement and decreased reliance on Engineering for client configurations. This work is very much ongoing and we’re still in the midst of collecting hard data.
SAVED ENGINEERING TIME
By empowering Implementations, CTS (Client Technical Support), and CS (Customer Support) with direct, granular control over authentication (SSO/MFA) and a new organization hierarchy (Client/Division), we eliminated the need for engineers to handle routine configuration changes, allowing them to focus on platform iteration.
STREAMLINED CLIENT ONBOARDING
The new portal architecture streamlined the creation and management of complex enterprise clients, ensuring faster and more accurate delivery of new customer environments.
REDUCED SUPPORT TICKETS
The release of core, user-validated features has decreased the volume of internal support tickets related to client setup and configuration errors that previously flowed into technical support queues.
IMPROVED SECURITY
The implementation of granular user group roles & permissions provided essential governance, assuring that internal admins only have the necessary scope of access required for their specific job function.
Learnings 🍎
The largest learning from this project was the power of deep, continuous collaboration with our subject matter experts, and the importance of designing for future self-service.
Design partnership is key: Since the platform is built for a highly specialized internal audience, working through OOUX workshops directly with stakeholder teams was non-negotiable. This early and continuous partnership ensured every workflow matched their day-to-day needs, preventing costly rework post-launch.
Prioritizing infrastructure first: The need to refactor and modernize the system to handle the parent/child hierarchy proved that investing in foundational, scalable infrastructure—even before designing the prettiest UI—is critical for long-term product health and enterprise success.
Designing for client self-service: We specifically designed the feature set and UI patterns with the ultimate goal of client delegation in mind. After successful internal use, feedback cycles, and iteration, this portal will be made available to client admins with specific roles assigned, removing the need for internal teams to handle routine configurations that clients can manage themselves.
